Why Apple wants to control developer beta distribution

It is perhaps not rocket science
Apple has apparently made moves to stop websites distributing developer beta versions of its software. There have been voices to condemn the move, but I think it makes sense to do so in the context of increasingly complex forms of attack.
Why Apple wants to control developer beta distribution
Apple has apparently leant on a couple of sites and required Twitter delete messages connecting people to places from which they can download its beta software, and/or developer profiles. It has not done so before, which implies it didn’t feel it needed to, so what has changed?
This is what has changed:
The security landscape.
Way back in time, researchers identified something called Xcode Ghost.
This was a fake version of Xcode that worked just like Xcode but shipped infected with malware that meant any application created in Xcode Ghost then carried malware to infect people’s machines. This was a bad thing, it allegedly impacted 128 million iOS users, but was dealt with moderately swiftly and the story kind of went away.
Then in 2021, a similar attack appeared, this time called XcodeSpy. This was a malicious Xcode project that installed a backdoor onto a developer’s Mac. It was once again a bad thing.
Imitation is not always flattery
Now, I’m not saying any of the sites that have been distributing Apple’s developer betas had anything to do with the latter attacks, but they are precisely the kind of outlets for software that can easily be created to distribute malware such as those XCode’s mentioned.
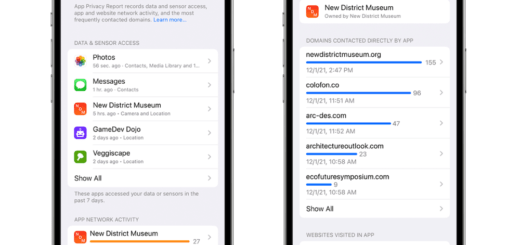
We also know that the threat environment is becoming far more complex. Apple knows this too. It knows that malware authors and others are kicking at the edges of all its security systems. It knows that impersonations and distribution of malware-infected versions of legitimate software (including operating systems) is a classic and time-honoured way malware authors have distributed their payloads. It also knows that its moves against semi-privatised surveillance entities such as NSO Group have raised its value as a target.
[Also read: NIST publishes essential macOS security guide for enterprise pros]
It’s within this context, I think, that Apple has decided to limit distribution of its operating systems within its own distribution networks. The fact it hadn’t done so until now means the company was prepared to exercise a little tolerance, but in the post-COVID, internationally tense era we now find ourselves in, even smaller security vulnerabilities need to be patched. And the last thing Apple needed was a site to distribute malware-infested versions of its hardware that carried or distributed malware once installed.
You got to stay aware
Trend Micro warns: “Attackers are starting to invest in long-term operations that target specific processes enterprises rely on. They scout for vulnerable practices, susceptible systems and operational loopholes that they can leverage or abuse.”
I don’t know for certain, no one has told me anything, but the move to prevent OS distribution outside of its official distro network strikes me as a decision that helps secure the company’s platforms. Which is something we always need to do.
Please follow me on Twitter, or join me in the AppleHolic’s bar & grill and Apple Discussions groups on MeWe.
Dear reader, this is just to let you know that as an Amazon Associate I earn from qualifying purchases.